YOUR CART
- No products in the cart.
Subtotal:
£0.00
BEST SELLING PRODUCTS
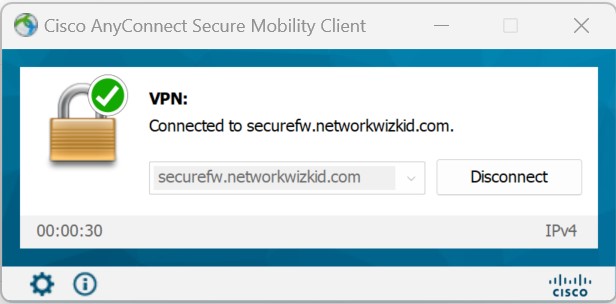
In this article we will take a look at how to configure Cisco Secure Firewalls for Passwordless Remote Access VPN authentication. Microsoft Azure will be used as the Identity Provider (IdP) and will also be federated with Duo for Single Sign-On (SSO) which will allow the use of Duo Passwordless.…
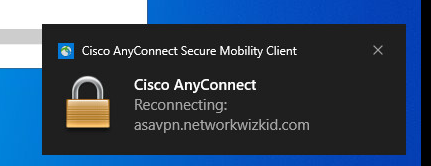
In this article, I will demonstrate how to configure a Cisco ASA for digital certificate-based authentication for remote access VPN users. Prerequisites Demonstration We will first start by downloading the Root CA which has been used to sign certificates associated with our remote access users and their devices. Once downloaded,…

In this post, we’re going to configure D-VTI and S-VTI between two CSR1000v routers to demonstrate hub and spoke deployments. The two devices used as shown in the topology below are R9 and R10. R9 will act as the hub and R10 will act as a spoke. Topology Devices R9…

In this post, we’re going to configure an IPSec site-to-site VPN with two CSR1000v routers. The authentication between the two routers will be performed using digital certificates issued from a separate Cisco CSR1000v router which is acting as a CA server. Topology Devices R12 – CA Server Configuration Configure Domain…

In the last post, we explored how to configure FlexVPN point-to-point IKEv2 S-VTI’s with preshared keys. In this post, we will do the same but this time using another CSR1000v acting as a CA server. This will allow us to authenticate each peer based on digitally issued certificates before the…
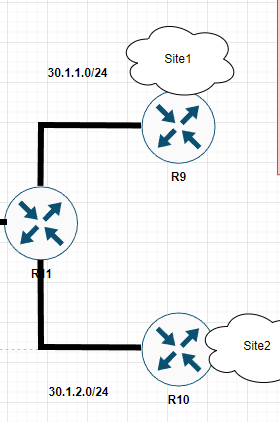
In this article, we’re going to configure a point-to-point IKEv2 Static Virtual Interface (S-VTI) between two Cisco CSR1000v routers using pre-shared keys as the authentication method. To demonstrate this, we’re going to use part of my lab topology as shown below. R9 and R10 will be used to configure IKEv2…