YOUR CART
- No products in the cart.
Subtotal:
£0.00
BEST SELLING PRODUCTS

Issue When attempting to log into a domain-joined Windows machine, the following error is presented: The error can be caused by a number of reasons, some of which are (but not limited to): Solution On the affected machine, remove the network connection and log in with the last known domain…

Over the years, organisations have been enticing their Facebook followers with opportunities to participate in giveaways, effectively leveraging social media for promotional purposes. Typically, users are required to engage with the content by liking, commenting, and sharing the respective Facebook post to enter these giveaways. While some pages genuinely conduct…
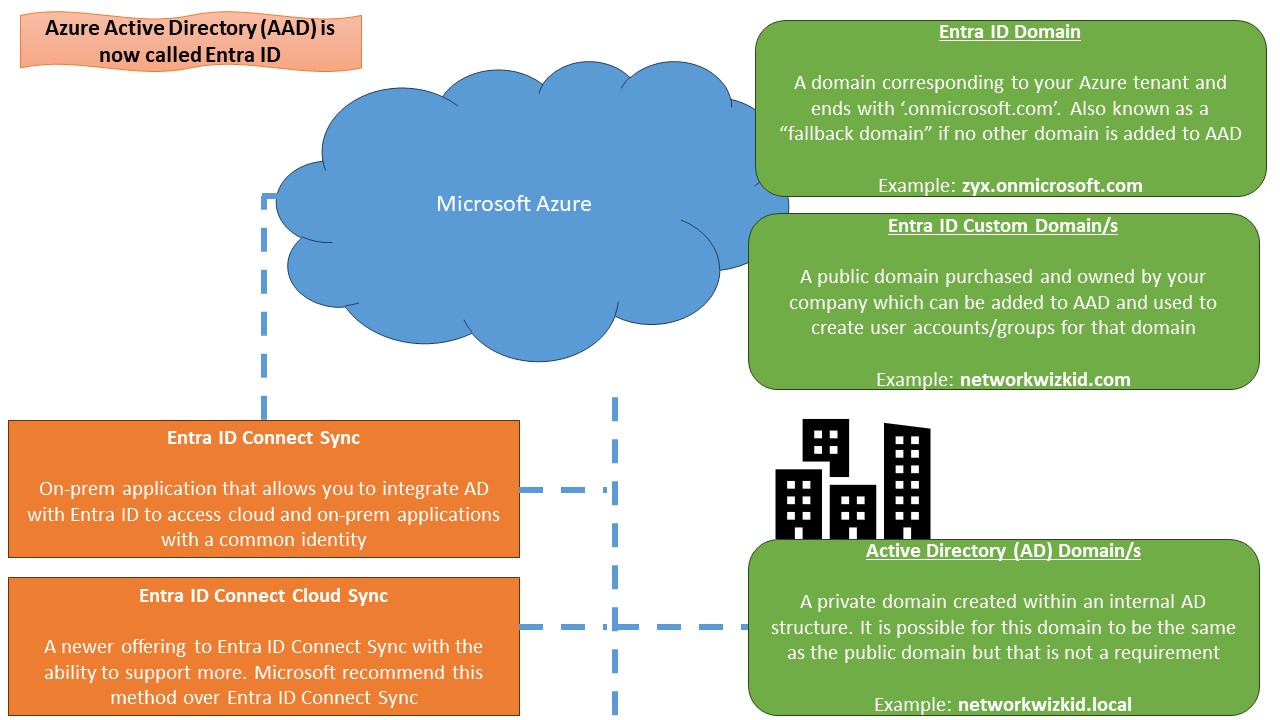
I engage in numerous conversations with customers on a daily basis, a significant majority of whom currently possess a hybrid infrastructure. While that is great, hybrid approaches also introduce the need to rethink traditional Identity and Access Management (IAM) solutions. Multiple, dispersed IAM solutions, while they work don’t deliver a…

In this article, we configure Dynamic Virtual Tunnel Interfaces (D-VTI) and Static Virtual Tunnel Interfaces (S-VTI) for a hub and spoke deployment. In the video demonstration, we use Cisco IOS devices complete with routing protocols BGP and EIGRP. Video Walkthrough Presentation and Topology Lab Device Configuration CSR Configuration