YOUR CART
- No products in the cart.
Subtotal:
£0.00
BEST SELLING PRODUCTS
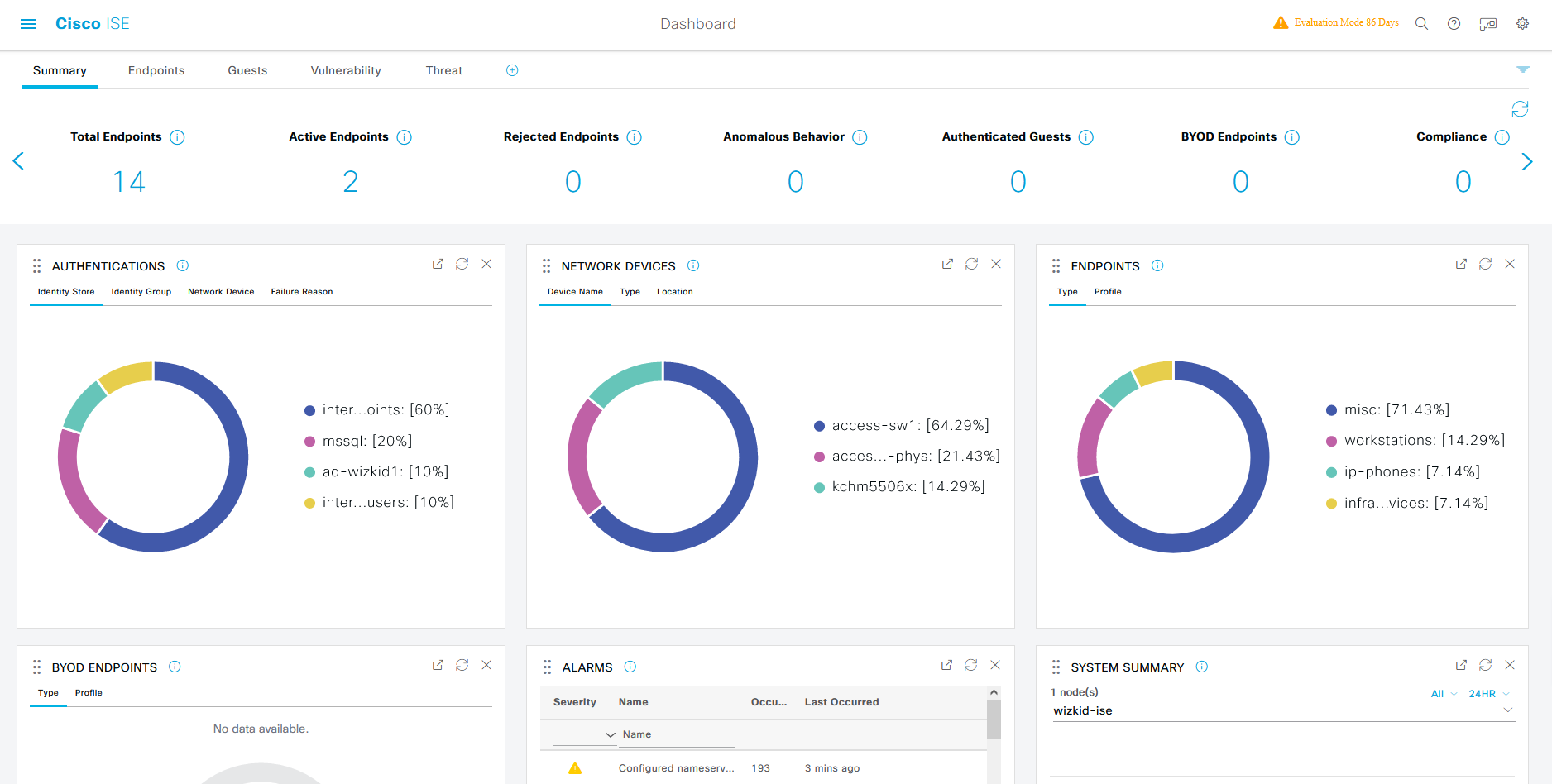
In this article, I would like to walk through the process of integrating the Microsoft SQL server with the Cisco Identity Services Engine (ISE). This is a recent piece of work that I have been exploring and not one that is very well documented at the time of writing this…

Ever thought about becoming a hacker and learning new skills in cybersecurity? Well, if you answered Yes then look no further because EC-Council, an educational cybersecurity company has opened applications to join their new $1 million scholarship program. This program will provide 2,000 qualified cybersecurity professionals with a place on…

ASA Configuration ASAv2 Omitted Configuration ASAv3 Omitted Configuration
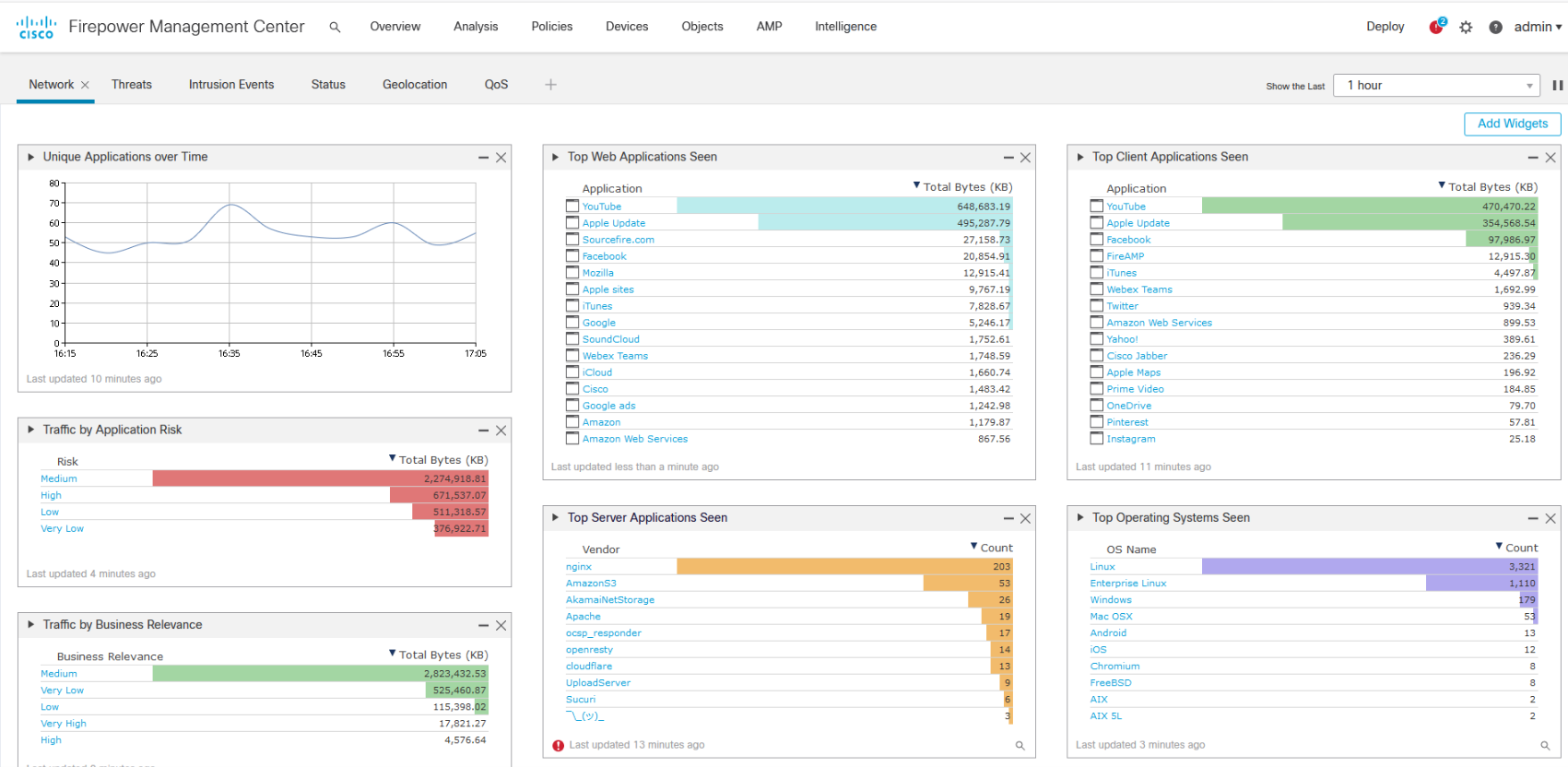
This is a quick article to highlight the potential interruption on Firepower devices caused by inspection interruption when updated are deployed to Firepower Threat Defense (FTD) devices. I will continue to update this article if/when more tests are carried out. Note: The following results may slightly differ in your environment.…

In this article we will analyse the behavior of Cisco ISE when configured as a distributed deployment. Furthermore, a series of failure scenarios will be carried out in an attempt to see how ISE functions when certain nodes are not available. The following tests could be useful in situations where…