In this demonstration, we will configure Duo two-factor authentication for Ubuntu servers.
Lab Set-up
- Ubuntu Server 18.04.4 (Bionic)
- Duo account
Add Local User Accounts
- If you have multiple user accounts that require access to the servers, create these users before adding Duo. These users will also need to be added to Duo too.
sudo adduser <name>
<Follow the instructions when shown>

Configure Duo
- Access Duo and select Applications > Protect an Application and search ‘UNIX Application‘ and click ‘Protect‘
- (Optional) Create any relevant policies for the new application
- Make a note of the following information as it will be required later:
- Integration key
- Secret key (Do not share)
- API hostname
Install Ubuntu Linux Packages
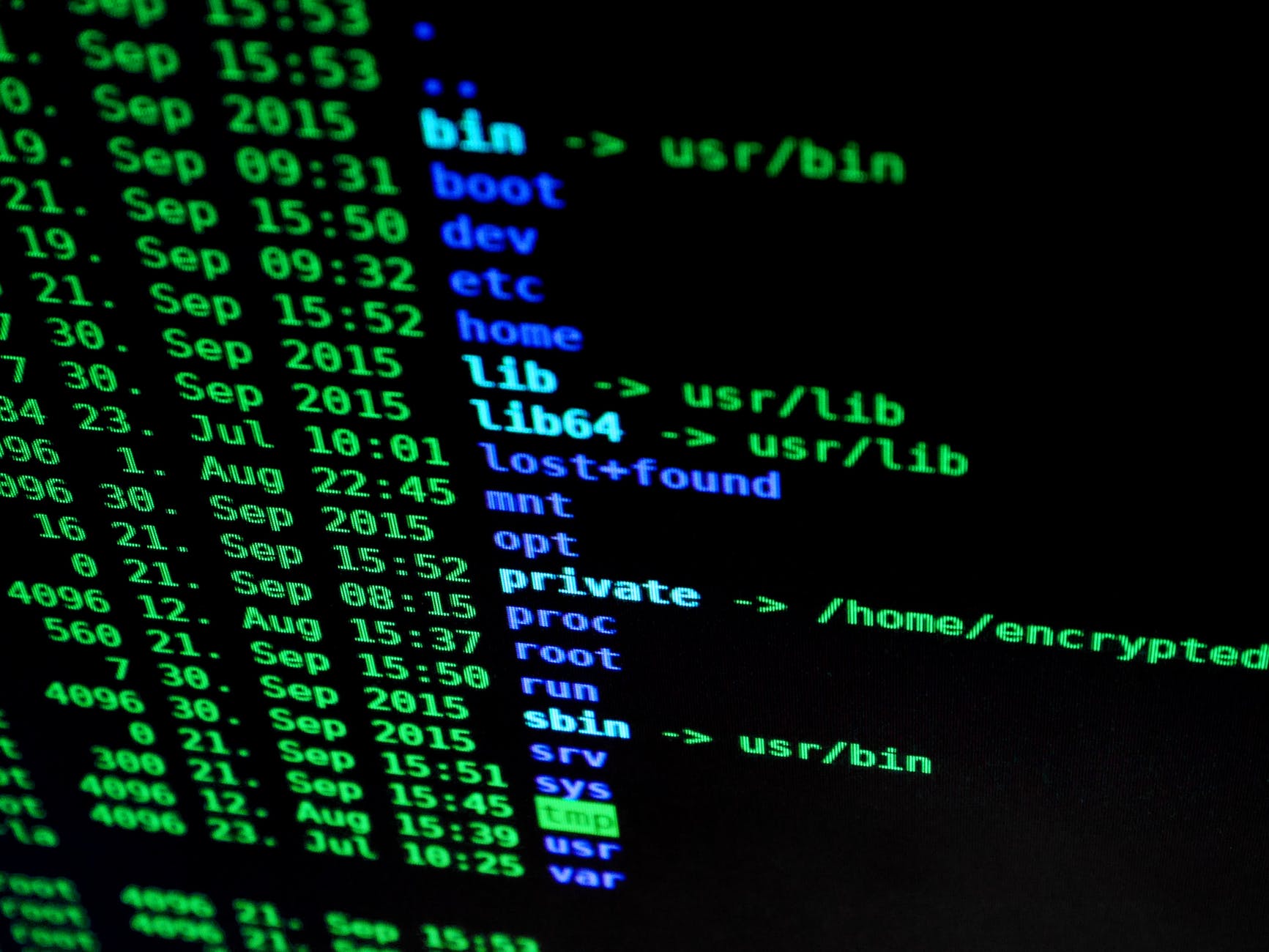
- Access the CLI of the Ubuntu system and enter the following commands. These will be used to install the Duo linux package.
nano /etc/apt/sources.list.d/duosecurity.list
deb [arch=amd64] https://pkg.duosecurity.com/Ubuntu bionic main
- Save and exit the editor
- On the CLI, execute the following commands
curl -s https://duo.com/DUO-GPG-PUBLIC-KEY.asc | sudo apt-key add -
apt-get update && apt-get install duo-unix
- The Duo Unix package is now installed.
Configure the pam_duo.conf File
To configure the pam_duo.conf file enter the following commands.
nano /etc/duo/pam_duo.conf
[duo]
; Duo integration key
ikey = <Enter your integration key>
; Duo secret key
skey = <Enter your secret key>
; Duo API host
host = <Enter your API host>
failmode = safe
; Send command for Duo Push authentication
pushinfo = yes
autopush = yes
- Save and exit the editor
For more information on Duo configuration file options click here.
Configure Public Key Authentication for Ubuntu Server in SSHD and Configure PAM
Enter the following commands.
Note: If you don’t want to configure public key authentication then ignore the last three commands.
nano /etc/ssh/sshd_config
ChallengeResponseAuthentication yes
UsePAM yes
UseDNS no
PasswordAuthentication no
PubkeyAuthentication yes
AuthenticationMethods publickey,keyboard-interactive
- Exit the editor and restart the sshd service by issuing the following command.
sudo systemctl restart sshd
Navigate to the pam.d common-auth and ensure that the following 4 auth fields are configured. Comment out anything else that is not already commented out.
In the configuration below, I have commented out with an #, the fields that were not required for this build.
nano /etc/pam.d/common-auth
# auth [success=1 default=ignore] pam_unix.so nullok_secure
# auth optional pam_cap.so
auth requisite pam_unix.so nullok_secure
auth [success=1 default=ignore] /lib64/security/pam_duo.so
auth requisite pam_deny.so
auth required pam_permit.so
- Save and exit the editor.
If using public-key authentication add the following commands.
Note: If you are not using public-key authentication but configure the following parameters you may experience strange behaviour when unenrolled users attempt to log in.
nano /etc/pam.d/sshd
auth [success=1 default=ignore] /lib64/security/pam_duo.so
auth requisite pam_deny.so
auth required pam_permit.so
Testing
Duo should now be successfully configured for 2FA. Without closing the currently open terminal proceed with the following tests.
- Create a new SSH session to your Ubuntu server
- Enter the username of the user. This user can be fully enrolled or partially enrolled into Duo
- Users that are fully enrolled will be automatically prompted to complete 2FA. However, users that are not yet fully enrolled into Duo will be prompted to enrol as shown in the screenshot below

Additional Information
If you experience multiple interactive keyboard sessions when trying to access the server and you aren’t using PKI with unenrolled users then you may have to check that you haven’t configured the public-key configurations.

Links
https://www.digitalocean.com/community/tutorials/how-to-set-up-ssh-keys-on-ubuntu-1804






Leave a Reply